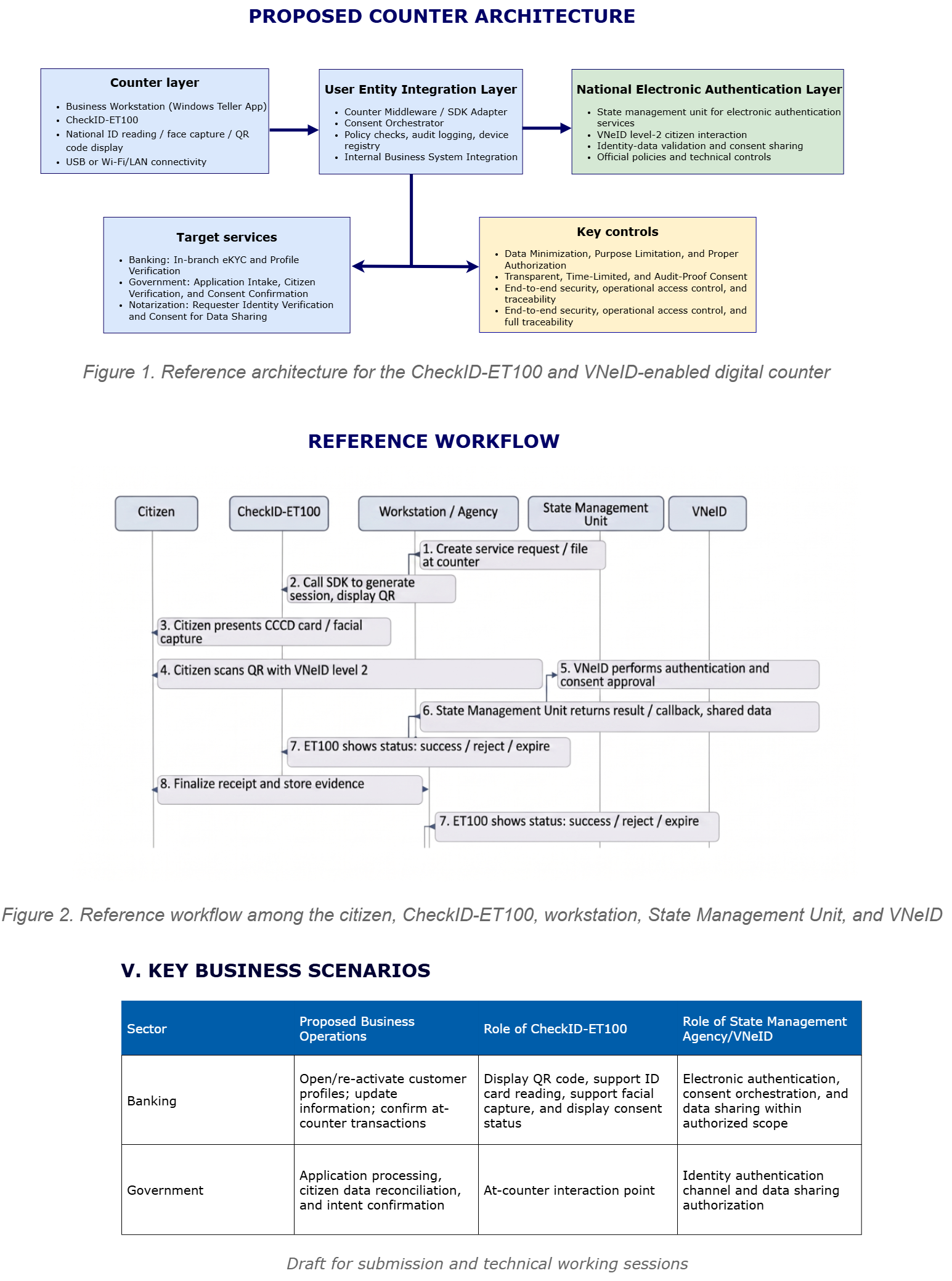
A practical implementation model that integrates CCCD card reading, facial authentication support, QR code display, and Level 2 VNeID consent orchestration into a single, unified, transparent, and controllable transaction journey.
Why This Topic Deserves Immediate Attention
At many transaction points today, identity verification, card reading, facial authentication, QR code presentation, and data-sharing consent processes are still performed in a fragmented manner. This leads to prolonged processing times, inconsistent user experiences, and increased complexity in process control when scaling up.
The proposed CheckID-ET100 solution offers a different approach to re-architecting the service counter as a unified digital interaction point. In this model, the counter device is no longer just supplementary hardware — it becomes the central display and orchestration interface that coordinates with the backend workstation to guide citizens through a seamless digital identity and consent journey.
From Fragmented Processes to a Unified Citizen Journey
The greatest strength of this approach is simplifying operations without compromising control. Instead of dispersing identity verification, authentication, and consent across multiple disconnected touchpoints, the digital service counter model consolidates the citizen-facing experience into a clear, guided flow, while backend integration and authentication remain anchored to official national infrastructure.
Reference Architecture: Practical, Controllable, and Scalable
Architecturally, the solution is organized into coordinated layers: the counter layer (CheckID-ET100 + workstation), the integration and consent orchestration middleware layer, the electronic authentication layer connected to state management authorities and VNeID, and the application layer serving banking, government, or notarization workflows.
A notable aspect of this approach is its strong emphasis on core principles such as purpose limitation, authorized access, transparent consent, data minimization, and privacy-by-design. As a result, it is not merely a UI improvement, but a robust, long-term foundation for digital trust operations at physical counters.
Immediate Value-Creation Scenarios
Banking and Financial Services
Ideal for high-assurance processes such as account onboarding, digital identity updates, customer verification at counter, and supervised digital consent collection.
e-Government Services
Supports document intake points where identity verification, transparent explanation of data usage purposes, and active citizen consent are all required.
Notarization and Legal Services
Particularly suitable for face-to-face transactions where strict identity verification, expression of intent, and evidentiary record-keeping are essential.
Governance and Security at the Core
One of the document’s strengths is its cautious and responsible approach. All information regarding APIs, callbacks, shared data, and consent mechanisms must strictly adhere to the scope permitted by competent authorities. This is essential for moving from a pilot concept to actual production deployment.
In terms of implementation, the system must clearly define requirements such as device registration, software and firmware inventory, transaction officer operation logs, temporary data management, and periodic review mechanisms before expanding the deployment scope. In other words, security is not an afterthought — it must be embedded in the design from the very beginning.
Pragmatic Roadmap: From Controlled Pilot to Scalable Deployment
A phased pilot program is far more appropriate than immediate large-scale rollout. This approach allows all stakeholders to refine business requirements, mature technical controls, and measure operational effectiveness before expanding to broader deployment.
Requirements and Scope Clarification
Align on business scenarios, target infrastructure, stakeholder roles, legal conditions, and pilot success metrics.
Detailed Technical Design
Standardize coordination between counter device, workstation, integration layer, consent mechanisms, logging, and security controls.
Limited Pilot Testing
Deploy at selected locations to measure processing time, system stability, user experience quality, and process completeness.
Evaluation and Scale-up Recommendation
Translate pilot results into technical, operational, and commercial recommendations for nationwide expansion.
A Stronger Message for the Market
CheckID-ET100 is not merely an additional counter device. Its greater value lies in transforming the physical service counter into a well-governed node within the national digital trust chain — capable of reading digital identities, supporting authentication, initiating consent, displaying status, and maintaining auditable records in a consistent manner.
From a market positioning perspective, this represents a powerful narrative for Mobile-ID: modernizing physical counters while maintaining strong control, traceability, and peace of mind for both citizens and service providers.
Suggested Positioning Message
Integrating digital identity, consent, and counter-assisted digital trust into one seamless transaction experience.







Community Discussion
Comments
Comments