Trusted PalmPay: building bank-grade biometric payment infrastructure with Mobile-ID
This article analyses Trusted PalmPay from a product and technical architecture perspective — covering how Mobile-ID combines identity, biometrics, digital wallet and banking connectivity capabilities into a deployable platform, as well as the expansion strategy suited to the realities of the Vietnamese market.
Overview: from a payment feature to a platform capability
Trusted PalmPay is the infrastructure where identity, biometrics, digital wallets, point-of-sale payments and banking connectivity are joined into a seamless journey that can be deployed in practice rather than remaining a technology demonstration.
What problem does Trusted PalmPay solve?
- Reduces friction at the point of payment for high-frequency, repeat-use cases.
- Creates an immediately visible innovation layer for banks at the point of sale.
- Enables consistent deployment of loyalty programmes, wallet top-ups, POS data analytics and cross-selling.
- Reduces reliance on mobile phones, QR codes or OTP at the counter.
What does Mobile-ID bring to this challenge?
- CheckID — onboarding, identity verification, eKYC and identity lifecycle management.
- Server-side biometric system — supports Palm Print/Palm Vein via Neurotechnology.
- Trusted Pay — payment orchestration, POS connectivity, notifications and settlement data.
- PKI / digital signatures — consent, mandate signing and bank-grade trust controls.
The Mobile-ID ecosystem in the Trusted PalmPay context
Trusted PalmPay’s advantage lies in the fact that Mobile-ID already has many foundational components that can be assembled into a complete architecture, shortening time-to-market and increasing credibility when engaging with a bank’s technical teams.
| Mobile-ID Component | Role in Trusted PalmPay | Value delivered |
|---|---|---|
| CheckID | Onboarding, eKYC, customer profile, biometric enrolment workflow, identity verification. | Establishes an identity layer and trust layer from the very start of the customer lifecycle. |
| Server-side biometric system | Template extraction, matching, scoring and policy signals for Palm Print/Palm Vein. | Enables genuine biometric deployment rather than stopping at the capture device. |
| Trusted Pay | Payment requests, POS connectivity, transaction status, refunds, dashboard and settlement data. | Directly connects the biometrics challenge to payment acceptance and POS operations. |
| PKI / Digital Signatures | Consent, mandate signing, API trust, device certificates and non-repudiation. | Elevates trust and meets bank-grade operational requirements. |
| Open Banking Integration | Top-ups, account linking, callbacks, reconciliation and settlement-related connectivity. | Transforms the solution from an internal wallet into a capability embedded within the banking system. |
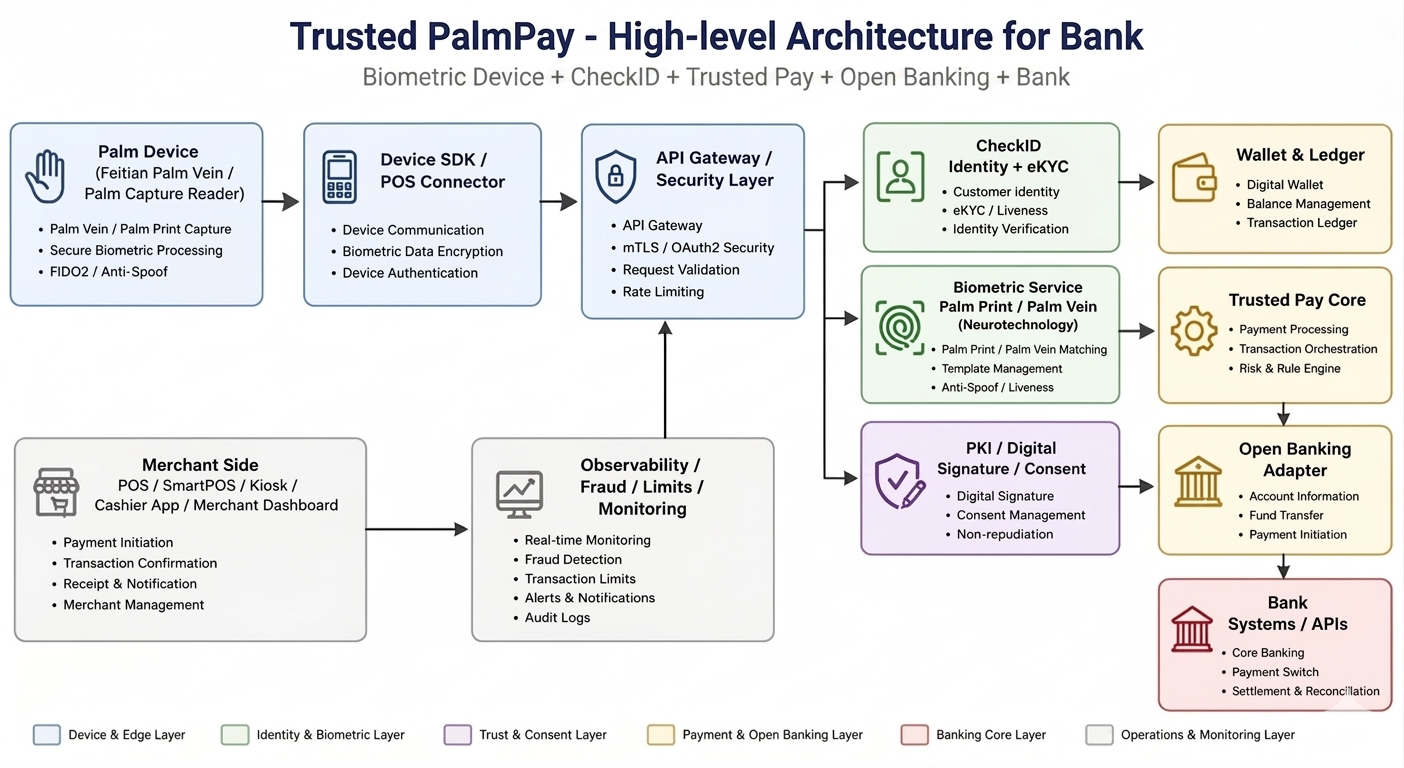
Overall architecture: why this solution is deployable
The Trusted PalmPay architecture is organised around a clear principle of layer separation. The device is responsible for capture, the server-side system is responsible for trust and transaction decisions, while the bank participates through funding rails and settlement.
Device and edge layer
The palm capture device serves as the contactless input point. This layer is suited to self-service kiosks, SmartPOS terminals, counter POS and controlled environments. Captured data is sent through the Device SDK or POS Connector for local quality checks and encryption before transmission to the server-side system.
API Gateway and security layer
The API Gateway is the backbone layer for authentication, authorisation, mTLS termination, rate limiting, audit headers and routing. Without this layer, the biometric benefits upstream are weakened by uncontrolled transport and integration risks.
CheckID and biometric service
CheckID handles customer identity, eKYC/liveness detection, profiles and verification context. The biometric service manages Palm Print/Palm Vein matching, template management and server-side anti-spoofing/liveness policies.
Wallet, Trusted Pay and Open Banking
The Wallet & Ledger manages balances, holds, debits, credits and refunds. Trusted Pay handles payment orchestration and the risk/rule engine. The Open Banking Adapter connects to bank APIs for account information, fund transfers and payment initiation as required.
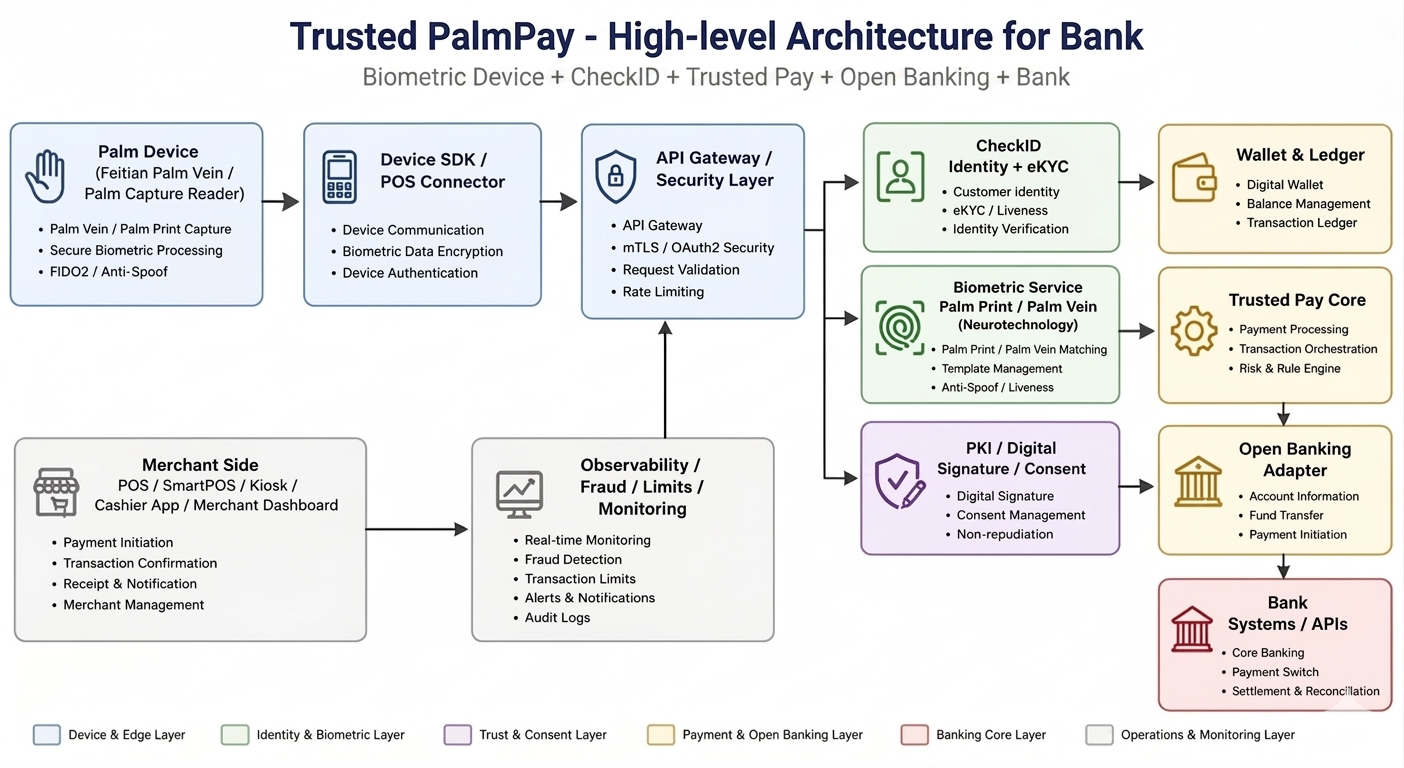
Deployment and trust zones: working with a bank’s CTO and security team
A compelling architecture diagram must demonstrate clear trust boundaries, the responsibilities of each deployment zone and how risk is controlled across the POS edge zone, the Mobile-ID platform, the integration zone and the banking zone.
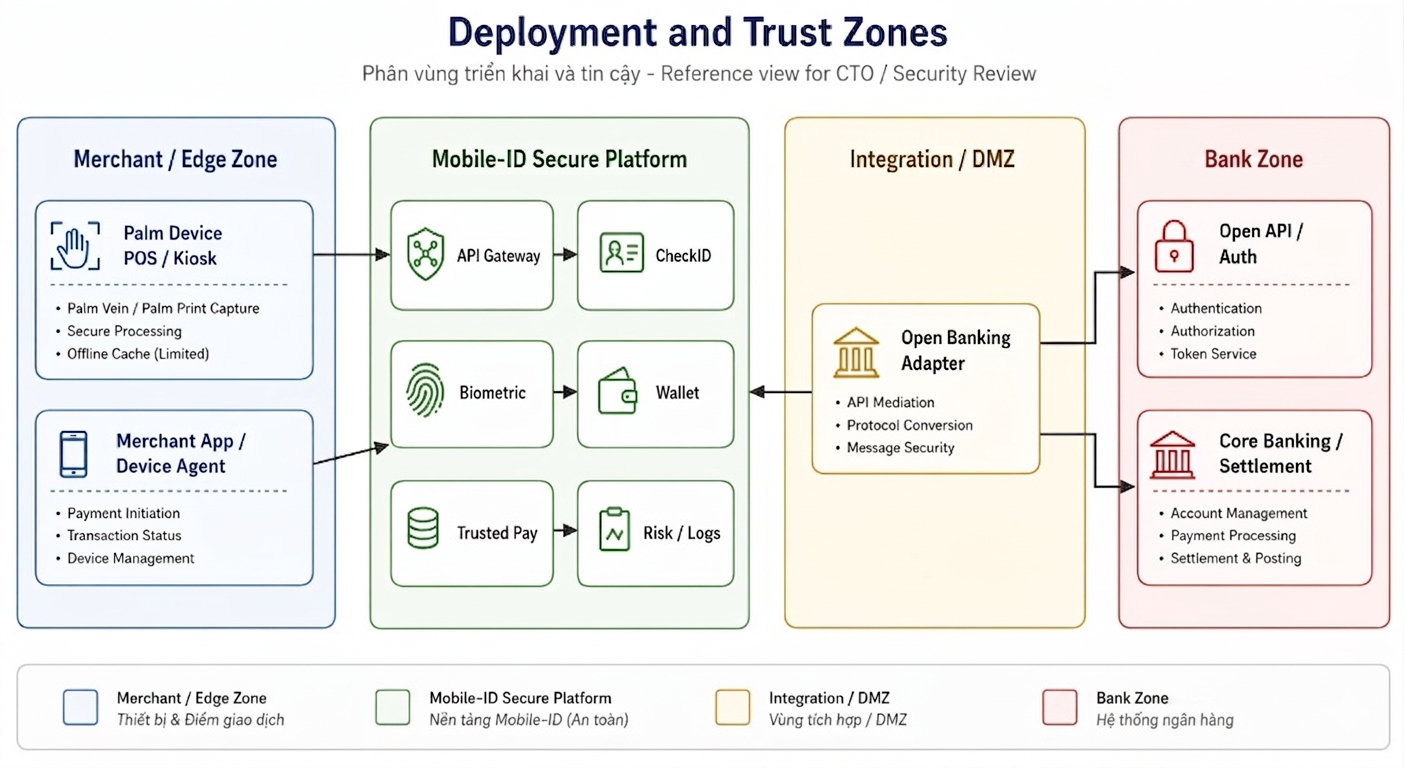
Why do trust zones matter?
- Reduces blast radius when an incident occurs in one layer.
- Simplifies access control and access to sensitive data.
- Clarifies the boundary of responsibility between the POS, Mobile-ID and the bank.
- Easier to audit during security and compliance review sessions.
Recommended deployment principles
- Treat devices as trusted endpoints requiring continuous verification, not unconditional trust.
- Separate the biometric domain from the wallet ledger domain.
- Keep critical transaction flows explicit and auditable.
- Prioritise the payment path through the wallet at POS; the bank primarily serves top-up, settlement and reconciliation.
Transaction flow: how the payment experience is created
A palm payment experience is only convincing when the transaction flow is designed to be concise, clear and equipped with fallback options. A well-designed processing sequence must show both the customer journey and the server-side decision logic.
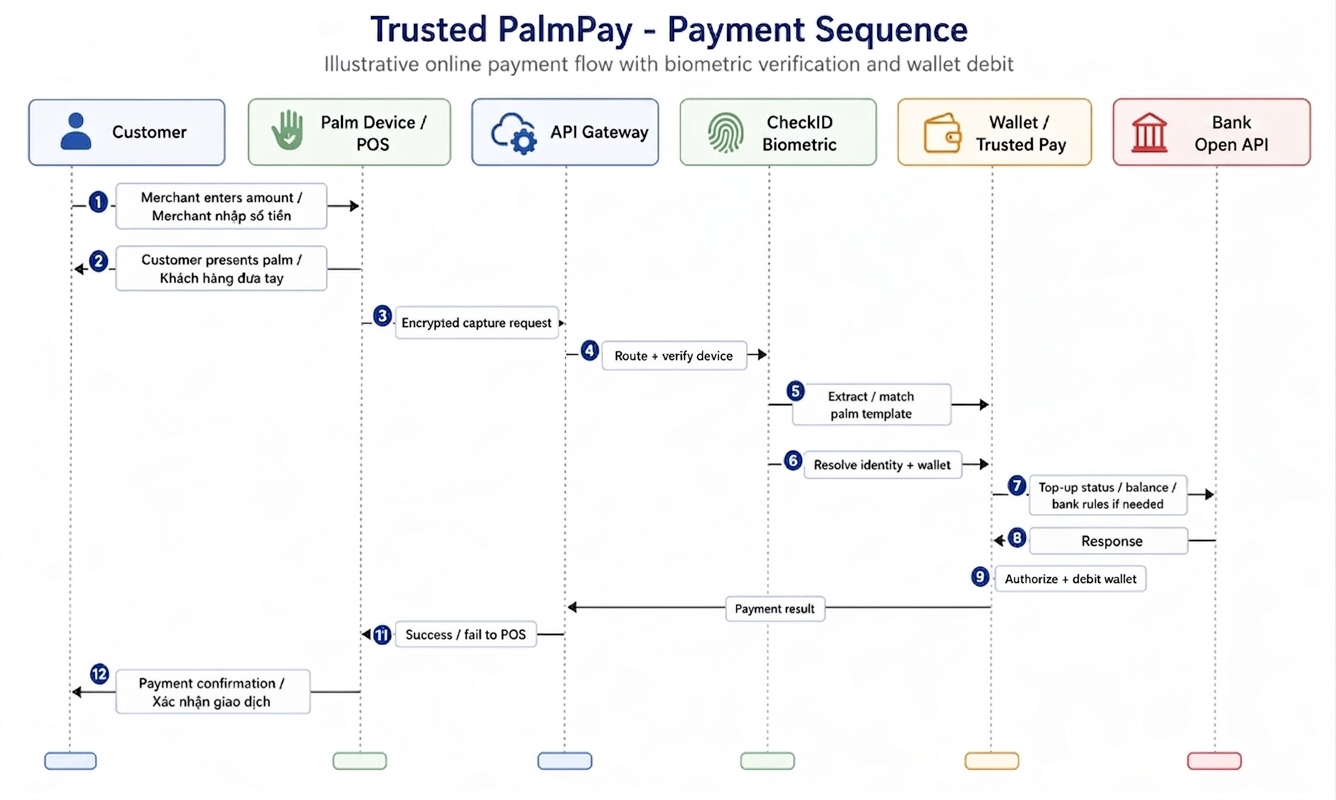
| Processing Step | Business Description | Technical Significance |
|---|---|---|
| POS enters amount | The cashier enters the transaction amount on the POS terminal. | Initiates a payment request on the POS side. |
| Customer presents palm | The customer places their hand within the device’s recognition zone. | The device captures a biometric dataset for transmission to the server. |
| Encrypted capture request | The Device SDK / POS Connector sends an encrypted request. | Protects biometric data before it enters the trust layer. |
| Routing and device verification | The API Gateway authenticates the calling channel and routes the request. | Controls device trust, session and security headers. |
| Template extraction and matching | The biometric service performs palm extraction and matching. | Returns the match result, score and policy signals. |
| Identity and wallet resolution | The match result is linked to the customer profile and digital wallet. | The step that connects customer identity to the transaction’s money movement. |
| Authorisation and wallet debit | The Wallet / Trusted Pay approves and records the transaction. | Reduces dependency on the bank’s real-time processing latency at POS. |
| Payment confirmation | The result is returned to the POS and the customer. | Closes the user experience loop in real time. |
Vietnamese market analysis and deployment strategy
Vietnam combines three favourable conditions for earlier adoption of palm payment than many other markets: established digital payment habits, a rapidly maturing digital identity infrastructure, and banks increasingly seeking payment models deeply integrated into their own ecosystems.
From QR codes to frictionless payment
QR codes have already educated the market on digital payments. The next step is reducing the number of actions at the counter for high-frequency, repeat use cases, where speed and convenience create a clear competitive advantage.
From eKYC to identity-driven payments
Having invested in building eKYC capabilities, the logical next step for banks is to reuse that identity capability for transactions, rather than limiting identity to the onboarding stage alone.
From innovation showcase to sustainable economics
Technology is only sustainable when tied to wallet balances, POS fees, loyalty programmes and cross-selling. Trusted PalmPay has an advantage because it can attach multiple value layers to a single transaction journey.
Recommended deployment roadmap
-
Pilot in a controlled environment — university campuses, corporate canteens, hospitals or industrial zones. These environments have repeat users, are easy to measure and carry low operational risk.
-
Wallet-first at POS — use Open Banking primarily for top-ups and settlement, avoiding dependency on the bank’s real-time processing latency at the point of payment.
-
Selective POS rollout — prioritise locations with high payment throughput and a clear pattern of returning customers.
-
Define success criteria upfront — active users, transaction success rate, false reject rate, top-up conversion rate and POS transaction throughput.
-
Expand by value layer — payments first, then loyalty/membership, then cross-selling and data analytics.
Priority use cases
| Use Case | Why it fits | The bank’s role |
|---|---|---|
| University campus / canteen | High-frequency repeat users; pilot results can be demonstrated in a short timeframe. | Funding rails, linked wallet, innovation brand positioning. |
| Hospital / clinic | Identity and payment can be naturally linked within a single service journey. | Bank account linkage, patient wallet, settlement reporting. |
| Corporate campus | Clear B2B2C model; easy to integrate with payroll and employee services. | Co-branded wallet, payroll linkage, corporate banking tie-in. |
| Retail chain | High transaction volumes with strong loyalty and membership programmes. | Merchant acquiring, promotional funding and data analytics. |
Reference glossary
A list of technical terms and system names used throughout this article.
Conclusion
Trusted PalmPay should be positioned as a new payment and identity platform led by Mobile-ID — not a hardware feature or a standalone technology experiment.
The value of the solution stems from the fact that Mobile-ID already has all the components needed to turn “pay by palm” into a genuine operational capability: capture device, identity, biometrics, payment orchestration, digital wallet, trust controls and banking connectivity — all within a single, coherent architecture.
For the Vietnamese market, the right approach is to start with a controlled scope, measure rigorously and scale in phases. Once a bank can demonstrate that customers are willing to use identity-driven payment in a high-frequency, repeat-use environment, the remaining challenge becomes ecosystem expansion — no longer a question of whether the technology can work.










Community Discussion
Comments
Comments